Get to know the SPEAKERS
Meet the experts shaping cyber security today
Lee Felsenstein
Lee Felsenstein is an American computer engineer who played a central role in the development of personal computers. He was one of the original members of the Homebrew Computer Club and the designer of the Osborne 1, the first mass-produced portable computer.
Before the Osborne, Felsenstein designed the Intel 8080 based Sol-20 computer from Processor Technology, the PennyWhistle modem, and other early "S-100 bus" era designs. His shared-memory alphanumeric video display design, the Processor Technology VDM-1 video display module board, was widely copied and became the basis for the standard display architecture of personal computers.
"Homebrew Computing Club, Me and My Big Ideas, The History of Hacking"


Chris Wysopal (Weld Pond)
Chris Wysopal (aka Weld Pond) was an early and longstanding member of L0pht Heavy Industries, the Boston-based hacker collective that turned a chaotic loft full of scavenged hardware into one of the most influential security labs of the early Internet. In the 1990s, he and his peers weren’t working from textbooks or corporate playbooks—they were pulling systems apart, finding where they broke, and publishing what they found, whether vendors liked it or not.
At the L0pht, Chris was part of the crew that helped turn vulnerability research into something public and impossible to ignore. From cracking password systems to exposing fundamental flaws in widely deployed software, the group’s work and tools like L0phtCrack forced a reluctant industry to confront the reality that insecurity wasn’t an edge case, it was the default.


They rejected “security through obscurity” and instead made disclosure a lever to shift power, dragging uncomfortable truths into the open.
He was part of the L0pht team that testified before the U.S. Senate in 1998, delivering the now-infamous warning that they could take down the Internet in 30 minutes, a moment when hacker knowledge collided directly with national policy. After the L0pht era, Chris co-founded Veracode, helping bring application security into the enterprise, but his roots remain in that original scene: a time when a handful of hackers, working outside the system, forced the system to change.
"The Accidental Cyber Think Tank:
How the L0pht Forced the World to Take Software Security Seriously"


G. Mark Hardy
G. Mark Hardy serves as President of National Security Corporation and co-host of the award-winning CISO Tradecraft podcast. He has been providing cyber security expertise to government, military, and commercial clients for over 40 years, and is the author of over one hundred articles and presentations on security, privacy, and leadership. A graduate of Northwestern University and Loyola University, he holds a BS in Computer Science, a BA in Mathematics, a Masters in Business Administration, a Masters in Strategic Studies, and is designated as a Certified Information Systems Security Professional (CISSP) and Certified Information Security Manager (CISM).
"A Hacker Looks at 50"
Richard Thieme
Richard Thieme (www.thiemeworks.com) is an old dog who is always learning new tricks. He is an author and professional speaker who speaks professionally about the challenges posed by new technologies and the future, how to redesign ourselves to meet these challenges, and creativity in response to radical change. He has published hundreds of articles, dozens of short stories, eight books and five anthologies, and has delivered hundreds of speeches. His pre-blog column, "Islands in the Clickstream," was distributed to thousands of subscribers in sixty countries before collection as a book in 2004. When a friend at the NSA told him, "The only way you can tell the truth is through fiction," he returned to writing fiction, incouding the Mobius Trilogy has been lauded by "insiders" at CIA, DIA, and NSA. He spoke in 2025 at Def Con for the 27th time. He has keynoted security conferences in 15 countries and clients range from GE, Microsoft, Medtronic, Bank of America, Allstate Insurance, and Johnson Controls to the NSA, FBI, US Dept of the Treasury. Los Alamos Lab, the Pentagon Security Forum, and the US Secret Service.


"I began addressing the human impacts of technological change--specifically the arrival of the public internet--32 years ago"


Johnny Shaieb
Johnny Shaieb is currently working on his PhD at the University of Tulsa, where his dissertation focuses on vulnerability database history and scoring. He is the Global Delivery Leader and Chief Architect of IBM’s Cyber Threat Exposure Management practice, an elite unit specializing in penetration testing, adversary simulation, and vulnerability management. His cybersecurity journey began in 1998 at WorldCom after earning a bachelor’s in management information systems from Oklahoma State University. He later pursued a master’s in Telecommunications at OSU and a second master’s in Computer Science at the University of Tulsa, focusing on NSA CyberCorps security.
With over 25 years of experience, Johnny has honed his offensive security skills through academic and professional endeavors. Since 2011, he has taught ethical hacking at institutions like Houston Community College and created the "Hac-King-Do" framework for free ethical hacker training. At IBM, he patented a methodology to automate hacker research and co-founded the X-Force Red Hacker internship with "Space Rogue" to recruit top cybersecurity talent.
"Axiomatic Events that Evolved Vulnerability Databases"
Andrew Brandt
Andrew Brandt has a 20+ year history in cybersecurity. He has served as a director of threat research at Symantec, Blue Coat Systems, and as a principal researcher at Sophos and Netcraft. Prior to working as a threat researcher, he was an investigative journalist and editor at PC World and a production coordinator for the syndicated TV show Next Step, dating to the mid-1990s. He has been involved in the hacking community since then as well, as one of the original members of San Francisco's Otaku Patrol Group. Brandt holds a deep and abiding affection for retrocomputing and retrogaming, and volunteers as a docent and retro-to-modern data specialist for the Media Archaeology Lab, based in Boulder, Colorado. The MAL houses the largest collection of functional retrocomputing devices, in a university laboratory setting, in North America.
"Bring Me (Back) To Life: Running early hacking tools on obsolete computers"


Heidi and Bruce Potter
Bruce and Heidi Potter have been building security technology and community for a long (long) time.
Bruce has spent nearly 30 years in cybersecurity, including founding The Shmoo Group and multiple stints as a CISO (pronounced “ciz-oh,” he’s not flexible on this). He started Turngate, his most recent adventure, as a bit of a passion project and now spends his time wrangling SaaS and AI security problems. Bruce also picks up new hobbies faster than he can get good at them.
Heidi is Turngate’s COO and the engine that keeps the company running. She previously ran ShmooCon, helping grow it into one of the most loved hacker conferences out there by keeping it welcoming, a little weird, and just organized enough. If something feels effortless, that’s Heidi putting in the effort behind the scenes. If it feels slightly chaotic…also Heidi, but very much on purpose.
Together, they’ve spent years building not just tools, but community by creating spaces where people can learn, connect, and debate important topics like security…or how to pronounce CISO (still “ciz-oh”). Outside of work, you’ll often find them walking or biking together. Otherwise, Bruce can probably be found dreaming up his next big hobby, while Heidi helps make sure it’s actually achievable.
"AMA with the Potters"
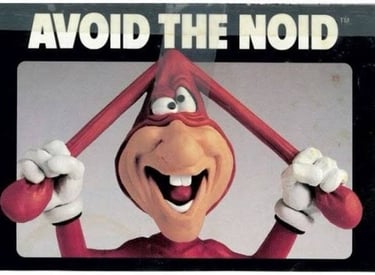
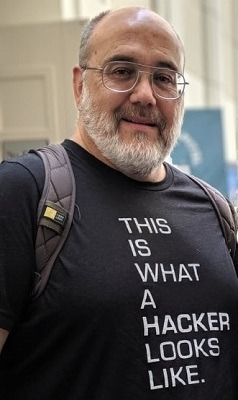
Brian Harden (noid)
Noid has spent his life building. From organizing the Los Angeles 2600 meetings in the 90’s, to building out the DC206 in the early 2000’s, to helping create the juggernaut that is DEF CON, Noid has built communities everywhere he’s gone. Now largely retired from the scene, Noid spends his days working on his farm and writing about himself in the 3rd person
"Community Organizing Before Social Media… How we did it"

Izaac Falken
Izaac Falken is a hacker of the 1990s and beyond. He's mostly associated with 2600 Magazine and the radio program Off The Hook. This year will mark 30 years in professional computer security consulting.
"## The Persistent Antipattern'); DROP TABLE keynote; -- In-band Signaling"
Mei Danowski
Mei Danowski is the founder and principal of Natto Thoughts, an advisory firm specializing in strategic threat intelligence rooted in geopolitical, economic, social, cultural, and linguistic analysis. She is internationally recognized for her expertise in connecting cyber threats to broader geopolitical, economic, and cultural dynamics. Before founding Natto Thoughts, Mei supported various U.S. government organizations and held key positions in the private sector at Microsoft, Accenture, and Verisign.
"Subduing the Enemy Without Fighting:
Ancient Strategy and the Birth of China's Early Hacker Imagination"




B.K. DeLong (McIntyre)
B.K. DeLong (handle: McIntyre) was a staff contributor at Attrition.org from the late 1990s through the early 2000s. He served as sometimes-spokesperson for the project & one of a handful of volunteers responsible for capturing, verifying, and archiving web defacements during the mirror's operational period - a project that ultimately cataloged over 15,000 defaced sites, documented geopolitical hacktivism, and became an early proof-of-concept for open, community-run cyber threat intelligence. Today he works as a Product Owner and Lead Engineer in Enterprise Vulnerability Management, taking a risk-based approach to vulnerability mitigation & remediation and exposure management programs.
"In January 1999, a small group of volunteers at Attrition.org decided to do something no one else was doing systematically: capture and archive defaced websites"
Edison Carter
Old-school hacker and phone phreak from the '80s & '90s.
"Life in an Early 90's Hacker Group"


Jericho
Jericho has been poking about the hacker/security scene for over 33 years (for real), building valuable skills such as skepticism and anger management. As a hacker-turned-security professional, he has a great perspective to offer unsolicited opinions on just about any security topic. A long-time advocate of advancing the field, sometimes by any means necessary, he thinks the idea of 'forward thinking' is quaint; we're supposed to be thinking that way all the time. No degree, no certifications, just the willingness to say things many in this dismal industry are thinking but unwilling to say themselves. Professional 'between the line' reader, expert rabbit-hole follower. He remains a champion of security industry integrity and small misunderstood creatures.
"Life in an Early 90's Hacker Group"



Josh Corman
Josh Corman is what you get when you put a wannabe superhero & formally trained philosopher into the hacker culture for ~30 yrs… As technology shifted from issues of bits & bytes to those of flesh & blood, he started leaning more into public policy and the public good on issues like the rise of Anonymous While some A-list 1337 hackers didn’t like that very much, in 2013, Josh launched “I am the Cavalry” to focus on over-dependence on undependable things… both the make things safer - and to make it easier for good faith hackers to do their part to help. Initially mocked, their approach helped build trust, open collaborations, soften postures towards good faith hacking, and even passed a few laws.
Josh lives in a few worlds, but often helps the outside world see the best hackers have to offer - and maybe also help hackers see the best in themselves. In day jobs he has oscillated between AppSec, CTO, Chief Security Officer roles… but has also done two stints at public policy think tanks and designed/implemented the CISA COVID Task Force in support of Operation Warp Speed. He is currently driving UnDisruptable27 to prepare for disruption to US Water and Hospital Access related to a Taiwan Conflict. He tilts at quite a few windmills… but some of them were dragons… and some of them were slain…
"Smashing the (Policy) Stack for … Public Safety & (Not) Profit?!"


Casey John Ellis
Casey is a serial entrepreneur and executive, best known as the founder of Bugcrowd and co-founder of The disclose.io Project. He is a 25+ year veteran of information security who grew up inventing things, hacking things, and generally getting technology to do things it isn't supposed to do. Casey pioneered the crowdsourced security as-a-service model, launching the first bug bounty programs on the Bugcrowd platform in 2012, and he co-founded disclose.io vulnerability disclosure standardization project in 2014 prior to its launch in 2018.
He’s an active member of a variety of policy and threat intelligence working groups and think tanks such as the Hacking Policy Council and the Election Security Research Forum.
He has personally advised the US White House, DoD, Department of Justice, Department of Homeland Security/CISA, the Australian and UK intelligence communities, and various US House and Senate legislative cybersecurity initiatives, including preemptive cyberspace protection ahead of the 2020 and 2024 Presidential Elections, the US National Cyber Strategy, and a variety of policies and EO’s relating to security research, anti-hacking law, and artificial intelligence.
Casey, a native of Sydney, Australia, is based in the San Francisco Bay Area.
"Smashing the (Policy) Stack for … Public Safety & (Not) Profit?! "
Jamie Arlen
Jamie Arlen brings a mix of security and engineering background to * as a service. Over the past thirty plus years, Jamie has been delivering information security solutions to Fortune 500, TSE 100, and major public-sector organizations. Jamie is best described as: “Infosec geek, hacker, social activist, author, speaker, and parent.” His areas of interest include organizational change, social engineering, blinky lights and shiny things. Greatest hits from the past include: Contributing Analyst at the research firm Securosis, blogger/podcaster with Liquidmatrix Security Digest, a frequent speaker at industry conferences, and a prolific contributor to media and standards including a lead author contribution to the Cloud Security Alliance Security Guidance for Critical Areas of Cloud Computing V4.


"FAIL: An epic career of doing all the wrong things and somehow still being right"
Fireside Chats
Meet your story tellers around the fire while they reminisce about history and hacking


Hack Beer'd
Cap'n HackBeer'd be the most infamous hacker buccaneer to ever hoist the Jolly Roger! Born during a Cat 5 hurricane, he built his first computer from a ship’s wheel and abacus before he could walk the plank. He scored his first dubloons from cracked software on the high C:\. He wears an iPatch on Tuesdays and his Peg Leg rebroadcasts MLB games with implied oral consent.
Legend has it his 1337 crew has SYNned in all 65,535 ports but never attACKed an honest sailor. Though he has a Bug Bounty on his head, his ship the Error 404 shall ne’er be found—disappearing into the vaporware or attacking alongside his first mate, Bobby TABLES, and his parrot, Pollymorphic.
"Avast, ye LAN lubbers! Grab a grog and park yer ParrotOS while cap'n HackBeer'd tells a `tail -f /dev/urandom`."


Edison Carter
Old-school phone phreak and hacker. Got started in the mid-80s, and active until the mid-90s.
"Digital Hooligan:
Origin and Exploits of an Old-School Hacker and Phone Phreak"


Dustin Heywood
Dustin Heywood otherwise known as EvilMog is a Senior Technical Leader at IBM X-Force, a semi retired member of Team Hashcat, and a Bishop of the Church of Wifi, he is a multi time Hacker Jeopardy World Champion and a collector to Black Badges.
"The early Hashcat beta days, the rise of the Alberta Hashcat super cluster, DROWN [..]"
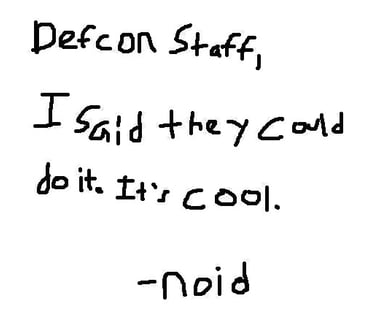
Brian Harden (noid)
Noid has spent his life building. From organizing the Los Angeles 2600 meetings in the 90’s, to building out the DC206 in the early 2000’s, to helping create the juggernaut that is DEF CON, Noid has built communities everywhere he’s gone. Now largely retired from the scene, Noid spends his days working on his farm and writing about himself in the 3rd person
"DEFCON War Stories with Unkie Noid"
Jeff Mann
Jeff is a respected Information Security advocate, advisor, hacker, evangelist, mentor, teacher, international keynoter, speaker, co-host on Paul's Security Weekly, four time Tribe of Hackers (TOH) contributor, and a member of the Cabal of the Curmudgeons. Jeff currently serves as a PCI QSA and Trusted Advisor, an Advisory Board Member for the Technology Advancement Center (TAC), and is the Director of Diversity, Equity, and Inclusion for Hak4Kidz NFP. He has over 40 years of experience working in all aspects of computer, network, and information security, including cryptography, risk management, vulnerability analysis, compliance assessment, forensic analysis and penetration testing. Certified National Security Agency Cryptanalyst. Designed and fielded the first software-based cryptosystem ever produced by NSA. Inventor of the "whiz" wheel, a cryptologic cipher wheel used by US Special Forces for over a decade recently displayed at the National Cryptologic Museum. Honorary lifetime member of the Special Forces Association.Previously held security research, management and product development roles with the National Security Agency, the DoD and private-sector enterprises. Architect of the first penetration testing "red team" at NSA. For the past
thirty years has been a pen tester,security architect, consultant, QSA, and PCI SME providing consulting and advisory services to many of the nation's best known companies.
"Meanwhile at the NSA"
Connect
Brought to you by Pyr0, the founder of Skytalks
© 2026 Bravo 6 Events LLC. All rights reserved. NaClCON™ is a conference brand owned and produced by Bravo 6 Events LLC.